Crypter ou chiffrer ?
Divulgâchage : Parce que les mots, c'est important. Mais surtout parce que ceux-ci cachent une révélation hermétique qui transformera le simple novice en initié aux Arcanes de la sécurité informatique. Se tromper convoquera des esprits vengeurs. Car le bon mot n'est pas celui qu'on croit. Âmes sensibles, s'abstenir (vous êtes prévenus).
Notre histoire met en scène un des personnages folkloriques de la sécurité informatique que vous avez sans doute tous déjà rencontrés. Sinon, ce n'est qu'une question de temps...
Au détour d'une conversation banale, d'une vidéo de vulgarisation ou d'un post de blog anodin sur la sécurité des données, l'Invocation Interdite est prononcée (par inadvertance ou malice) et il répond à l'appel pour corriger l'innocent maladroit de son erreur indigne avant de repartir avec rage et dégoût à ses croisades purificatrices.
On dit chiffrer, et pas crypter. :-)
Dans le règne Daemonium (démons), il se classe chez les Troglodytam (Trolls), dans la famille des Impatiens Grammerian (communément appelés Grammar Nazi). Ce genre très spécifique sévit principalement dans des environnements naturels sécurisés et se reconnaît facilement à son appétit insatiable de cryptographie. Ou de cryptologie, car il y a plusieurs espèces qui cohabitent plus ou moins pacifiquement.

Les sujets possédés sont généralement jeunes (µ = 25 ans, σ = 2,5 ans) mais des textes sacrés suggèrent l'éventualité de possessions spontanées (i.e. sans invocation) à des âges bien plus avancés. La conjecture communément admise chez les spécialistes postule que ces Argentum Dorsum soient plus aguerris, plus puissants et donc capables de créer d'eux-mêmes une brèche dimensionnelle.
Il faut noter que le seul terme admis en français est celui de chiffrement.
ANSSI, « Mécanismes cryptographiques » du Référentiel Général de Sécurité, version 2.03, page 32. Disponible en ligne
Des recherches anciennes suggèrent l'influence d'un agent viral. En effet, tous les sujets possédés ont été préalablement en contact avec un autre sujet possédé symptomatique. Après une phase aigüe s'installe généralement une phase chronique avec des possessions invoquées dont la fréquence décroit avec le temps et ont fait longtemps croire à une possible réponse immunitaire. Cette exposition nécessaire n'est cependant pas suffisante, car de nombreux sujets ne développeront aucun symptôme par la suite.
Pour le novice, ces possessions sont troublantes. L'absence d'évolution suite à la possession montre une très claire parenté avec le non moins célèbre Punctum Deusvincit mais sa rapidité d'exécution laisse pantois. Le novice s'interroge sur son utilité ; pourquoi tant d'effort ? pourquoi tant de haine ?
Crypté ou encrypté Termes généralement utilisés par les personnes qui n'y comprennent rien. Vous devriez cesser de l'utiliser après la lecture de cet article.
Marc Framboisier (12 janvier 2018), « Cryptographie expliquée aux Michus » Disponible sur framboisier.com
Étymologiquement, on devrait dire crypter
Parce que le novice, comme son nom l'indique, n'est pas encore initié aux Arcanes, il base sa recherche spirituelle sur ses connaissances forcément parcellaires de la Sagesse Collective ce qui comprend bien évidement l'étymologie, ou l'art subtil de déduire le sens des mots de leur parenté avec des mots connus.
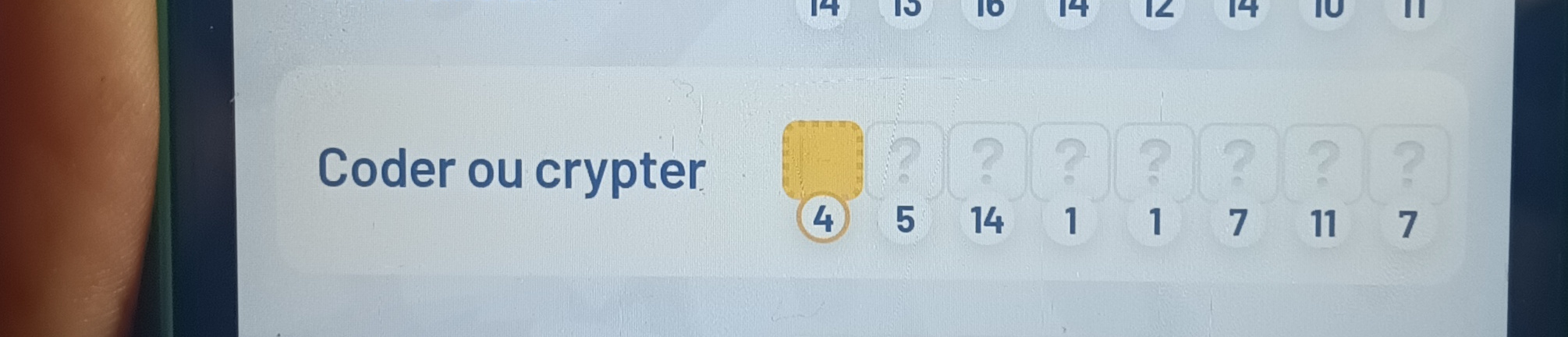
Coder, traduire en symboles
Le verbe français coder vient du verbe anglais to code qui vient lui-même de l'ancien français codex, dérivé du latin caudex qui veut dire (entre autres sens) un registre, un livre fait de l'assemblage de tablettes. Dans sa forme purifiée, coder a le sens suivant :
Traduire une information en symboles.
Lorsque nous parlons, lorsque nous écrivons, nous codons notre pensée en signes (sonores ou visuels) qui seront décodés par notre interlocuteur en pensées dans son esprit à lui (ou elle). Quelqu'un ne possédant pas la convention, c'est-à-dire le code, ne peut ni émettre ni recevoir d'information. D'où les efforts de tous les états qui se respectent pour enseigner leurs codes à leur population dès l'enfance.
Lorsque la convention est secrète, que le but est de restreindre la communication aux seuls initiés, on parle alors de code secret et il est aujourd'hui admis que c'est une mauvaise manière de procéder, car la protection du système tombe dès que la convention est connue, ce qui nécessite d'incessantes inventions de nouveaux codes et mise à jours dans la population cible.
Il en va ainsi des missives diplomatiques et militaires des siècles précédents ,mais également de certaines conventions sociales qui permettent à un groupe de se reconnaître par l'utilisation de codes plus ou moins subtiles (signes vestimentaires, d'accents, d'utilisation du subjonctif, orthographe...).
Crypter, rendre un message illisible
Le verbe crypter et l'action cryptage dérivent du latin crypta lui-même issus du grec ancien κρυπτός, un adjectif signifiant caché, secret. Il a donné par adaptation les termes de cryptographie (art de l'écriture secrète), cryptologie (science des messages secrets), cryptanalyse (art de casser les écritures secrètes), voire même des cryptomorphismes (des applications entre deux ensemble dont le principe d'action est loin d'être évidente). Dans sa forme pure, il a le sens suivant :
Modifier un message pour le rendre illisible à qui n'a pas le droit de le comprendre.
Ainsi, crypter à un sens plus général que coder. On peut crypter en codant, mais pas uniquement. On peut, par exemple, ajouter un bruit au message envoyé, le rendant illisible lors de la transmission, puis soustraire ce bruit à la réception pour découvrir le message caché (émetteur et récepteur doivent s'être mis d'accord au préalable sur le bruit à ajouter).
La cryptographie moderne rend bien compte de cette globalité. La protection des missives importantes impliquant des codes, des modifications du message et l'ajout de bruit, plusieurs fois et dans divers ordres.
Chiffrer, traduire en chiffres
Le verbe chiffrer en français vient du mot chiffre dérivé du latin médiéval cifra lui-même issus de l'arabe صفر qui veut initialement dire zéro. Dans sa forme pure chiffrer a le sens suivant :
Traduire en chiffres.
On le rencontre en gestion de projet lorsqu'on doit dire combien ça va coûter, en musique lorsqu'on écrit les accords et, pour ce qui nous concerne, en cryptographie lorsqu'on traduit un message en chiffres.
Le cas le plus emblématique est le Grand Chiffre inventé par Antoine Rossignol au service de Richelieu puis Mazarin. Il s'agit d'un répertoire de 587 nombres différents codant des syllabes (et parfois des mots) ainsi que quelques instructions destinées à gêner la cryptanalyse (i.e. « ignorer la syllabe précédente »).
Le verbe chiffrer est donc utilisé dès le XVIIème siècle pour décrire la transcription d'une information à l'aide de chiffres, c'est-à-dire à la coder en chiffre. En ce sens, chiffrer est plus restrictif que coder puisqu'on peut coder autrement qu'avec des chiffres.
En anglais
On pourrait croire que cette question épineuse est typiquement francophone, mais elle touche pourtant nos voisins anglophones qui disposent des trois mêmes nuances magiques :
- To code : pour coder, même racine latine,
- To encrypt : pour crypter, même racine grecque,
- To cipher : pour chiffrer, même racine arabe.
Et après
Lorsqu'on parle de rendre un message illisible pour qui n'en détient pas la clé (au sens métaphorique), l'Étymologie et la précision scientifique voudrait qu'on dise crypter mais ce faisant, on prend le risque de convoquer des esprits torturés qui veulent vous convertir au chiffrement et ainsi obtenir la paix intérieure à laquelle ils aspirent tant.
La diplomatie voudrait donc que vous disiez chiffrer au prix d'une dissonance cognitive plus ou moins prononcée en fonction du stade de conversion de votre auditoire. Chez des initiés ce mot vous fera reconnaître comme l'un des leurs mais vous risquez de perdre les novices qui vous écoutent (à moins que ce soit le but).
Alors que faire ?

C'est à vous de choisir en fonction de vos objectifs et du contexte de votre communication. Pour notre part, voici comment nous tranchons en fonction de l'auditoire.
Lorsque nous vulgarisons ou enseignons à l'école, l'auditoire veut comprendre comment le monde fonctionne. Nous disons alors crypter (et si on a le temps, on mentionne que certains disent chiffrer). Le but, c'est qu'ils comprennent et crypter est plus efficace pour y parvenir.
En enseignement supérieur, les élèvent veulent principalement un boulot à la fin de leur formation. Nous disons donc chiffrer (et si on a le temps, on explique le pourquoi du comment). Le but est qu'ils s'intègrent au monde du travail et chiffrer est plus efficace pour y parvenir.
Le reste du temps, nous n'y réfléchissons pas, car notre vie ne consiste pas à parler de cryptographie et surtout, nous partons du principe que chacun crypte ou chiffre bien ce qu'il veut.
Remerciements
Etienne Morin pour sa relecture (très) attentive.
Socialement, on devrait dire chiffrer
Si on s'attache au sens premier des mots, il est évident que crypter englobe coder qui englobe lui-même chiffrer et que la cryptographie consiste donc à crypter des messages...
Mais pourquoi donc ces forces obscures dépensent-elles autant d'énergie dans cette croisade si futile ? Tentez l'expérience si vous êtes joueurs : laissez traîner l'Invocation sur le Grand Internet, et Il viendra à coup sûr mordre à l'hameçon, parfois suivi de ses rejetons.
La version officielle
Comme vous vous en doutez, il y a plusieurs degrés dans l'horreur, plusieurs versions qui expliqueront les différences observées in vivo.
La norme ISO 7498-2. Qu'on pourrait qualifier de modérée. Publiée en 1989, puis revue en 2000, elle décrit les éléments généraux d'architecture informatique de systèmes sécurisés. Sa section 3 contient les fameuses Définitions.
Le RGS de l'ANSSI. Le Référentiel Général de la Sécurité a été publié bien plus tard ; la version 1 en 2010 et la version 2 en 2014. Il a le même but que l'ISO 7498-2 (fixer les éléments de référence) mais ces années de maturation ont enrichi ses réflexions hermétiques qui sont donc plus aiguisées.
Vous trouverez le Paragraphe dans l'annexe B1 (section A.1.1 en page 32) que nous reprenons ici in extenso pour ne pas en dénaturer le Message Révélateur :
L'exégèse de ce texte fondateur (car cité comme référence lors des corrections francophones) est fournie dans le tableau suivant où, pour chaque terme vulgairement utilisé, correspond le terme officiel du mythe.
Le novice fera rapidement remarquer le glissement de sens pour décrypter dans la version officielle (et se demandera si crypter décrit l'opération inverse, à savoir chiffrer sans connaître la clé), ainsi que l'incohérence des radicaux, tantôt grecs (crypt), tantôt arabes (chiffre) et qu'en toute logique linguistique, la science du chiffre devrait s'appeler la chiffrologie.
Certaines légendes interdites mentionnent des novices qui se sont égarés en remarquant que la justification du verbe chiffrer viendrait du fait d'utiliser des opérations mathématiques...
D'autres égarés ont ensuite fait remarquer qu'un chiffre est un glyphe sans signification et que les mathématiques traitent de la Théorie des nombres (du latin numerus). Ils ont alors émis l'hérésie audacieuse que puisqu'il s'agissait d'effectuer des opérations mathématiques sur des nombres issus de textes, en toute logique, on devrait donc parler de numérologie...
Mais il s'agit là d'une réduction simplificatrice qui ignore tout de la subtile complexité cryptologique et démontre surtout chez leurs auteurs, comme nous le verrons dans la suite, d'un manque d'études approfondies ou de leur limitation cognitive (voir les deux).
Un marqueur social
Dans sa bible « Applied Cryptography », Bruce Schneier tente d'expliquer la victoire de chiffrer sur crypter qui rappelant la crypte (lieu où on cache des défunts) invoquerait l'image de cadavres et choquerait ainsi certaines cultures...
Notre interprétation est beaucoup plus simple et suit un avis généralement partagé comme le relate spontanément ce témoin de nombreuses possessions :
L'utilisation du Langage officiel du Mythe ne cache donc pas une meilleure compréhension des Arcanes du sujet (en témoignent les incohérences internes au mythe) mais plutôt un moyen pour l'élite de se distinguer de la plèbe. Ce qu'on appelle communément en sociolinguistique un « registre de langue ».
Pour l'initié, ce shibboleth lui permet de déterminer avec exactitude la classe sociale de son interlocuteur sans que le novice s'en rende compte. Imparable.
L'assimilation d'un mythe
Apprendre le Langage officiel a un coût cognitif non négligeable. Contrairement aux termes vulgaires, qui sont tous construits logiquement à partir d'un préfixe commun, leur version officielle n'est pas cohérente ; certains mots changent de sens et plusieurs préfixes sont utilisés.
Il s'agit là de ce qu'on appelle une dissonance cognitive. Un état inconfortable dans lequel notre esprit se trouve lorsqu'il est confronté à une situation en contradiction avec ses cognitions. Pour retrouver la paix intérieure, il a besoin de résoudre le conflit.
Puisqu'il ne peut y en avoir qu'un, l'issue est manichéenne...
Soit le bon verbe est crypter. Et donc l'ANSSI, l'ISO, les enseignants et autres experts se trompent. L'étymologie et le marqueur social fournissent une explication simple et satisfaisante au phénomène, mais implique qu'utiliser crypter nous exclue du groupe dominant, ce qui sera d'ailleurs le cas.
Certains ermites empruntent cette voie et obtiennent la Paix Intérieure. Mais au prix de l'exclusion par leurs semblables. Pour ceux qui veulent travailler dans le domaine, ils devront apprendre à se travestir en disant chiffrer tout en préférant dire crypter et ça leur en coûtera. À chaque fois.
D'où l'intérêt économique de la deuxième solution.
Soit le bon verbe est chiffrer. Et il doit bien y avoir une raison, forcément. Certains se satisferont de suivre le dogme enseigné avec autorité. D'autres rechercheront des traces d'utilisations plus anciennes ou même des justifications plus ou moins ésotériques.
Dans cette voie, il y a adhérence au Mythe. Une fois converti, on se sent faire partie de la grande famille des experts en sécurité informatique, les élus détenteurs des Arcanes, illuminés par la Révélation. On sait quoi faire, c'est rassurant : Il faut dire chiffrer, car c'est le seul mot admi en français.
Au début, la présence de crypter génèrera un inconfort, résolu en la considérant comme la marque d'un novice. Puis, petit à petit, la résolution se fera automatiquement en ignorant cette erreur de l'interlocuteur et ainsi, avec le temps, l'initié est converti.
Prosélytisme missionnaire
Mais tant que la croyance est fragile, chaque Invocation Interdite rappelle la dissonance cognitive et l'inconfort correspondant. Chaque occurrence de crypter fait douter le novice, dans son parcours initiatique, l'obligeant à chaque fois à lutter contre l'Étymologie Hérétique.
Chez certains esprits, cette lutte permanente provoque une injonction missionnaire pour convertir la plus grande partie de la population païenne et les ramener dans la Vérité. Toutes les occasions sont utilisées pour transmettre le message officiel : articles de blogs, vidéos de vulgarisation ou même des normes et autres référentiels de sécurité.
Le missionnaire espère qu'une fois la population autour de lui convertie, n'entendant plus l'injonction, il trouvera enfin la paix à laquelle il aspire tant.
Mais cette voie est vouée à l'échec. Parce qu'avec Internet, c'est la planète entière qui vit autour de lui et le flot des novices est intarissable tant l'Étymologie est efficace. Il le sait et face à ce défi impossible, certains abandonnent la lutte.
D'autres, au contraire, redoubleront de dévotion.
Réactions stéréotypées
Que se passe-t-il donc quand un esprit dévot torturé par le doute rencontre l'injonction en ligne ?
Contrairement au monde réel où la peau fournit une frontière physique et psychique à son Être, tamisant les informations qui entrent ou sortent. Dans le cyberespace, l'information atteint directement sa conscience, sans interprétation, et surtout sans filtre.
Le blasphème est alors formulé dans l'esprit torturé comme s'il en émanait directement. À la dissonance cognitive habituelle s'ajoute cette fois la culpabilité d'avoir péché. La colère est trop grande et provoque une réaction de rejet et de destruction de cette pensée impure.
Et contrairement au monde réel où la peau contient les pensées violentes, dans le cyberespace, les intensions s'y expriment librement, sans retenue, et donc sans filtre.
C'est pour cela que l'invocation, prononcée dans le cyberespace, y trouve une telle caisse de résonance. Les possessions y sont non seulement plus faciles, mais aussi beaucoup plus nombreuses. Là où vous ne risqueriez qu'un regard courroucé dans une conversation mondaine, vous ferez cette-fois face à une véritable armée de cyber-spectres décidés à en découdre.